Notifications
Clear all
Topic starter
29/10/2022 7:07 pm
While conducting a network infrastructure review, a security analyst discovers a laptop that is plugged into a core switch and hidden behind a desk.
The analyst sees the following on the laptop's screen:
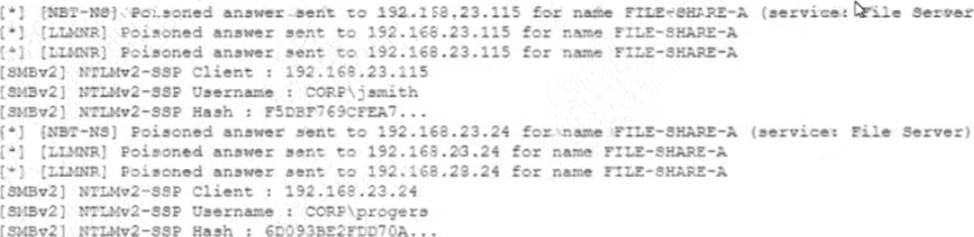
Which of the following is the BEST action for the security analyst to take?
- A . Initiate a scan of devices on the network to find password-cracking tools.
- B . Disconnect the laptop and ask the users jsmith and progers to log out.
- C . Force all users in the domain to change their passwords at the next login.
- D . Take the FILE-SHARE-A server offline and scan it for viruses.
Suggested Answer: D
