Notifications
Clear all
Topic starter
15/10/2022 11:19 am
Given the Cyber-Attack Lifecycle diagram, identify the stage in which the attacker can initiate malicious code against a targeted machine.
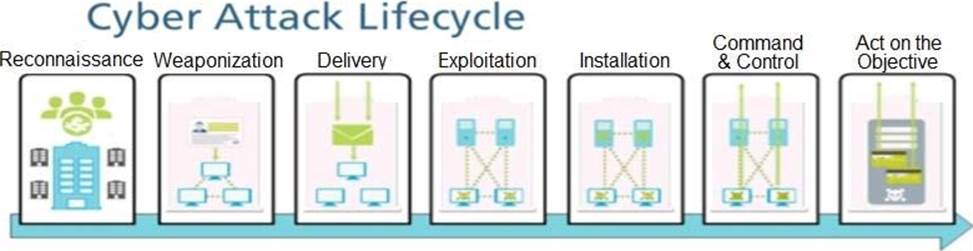
- A . Exploitation
- B . Installation
- C . Reconnaissance
- D . Act on Objective
Suggested Answer: A
