Notifications
Clear all
Topic starter
A security analyst is reading the results of a successful exploit that was recently conducted by third-party penetration testers. The testers reverse engineered a privileged executable. In the report, the planning and execution of the exploit is detailed using logs and outputs from the test However, the attack vector of the exploit is missing, making it harder to recommend remediation’s.
Given the following output:
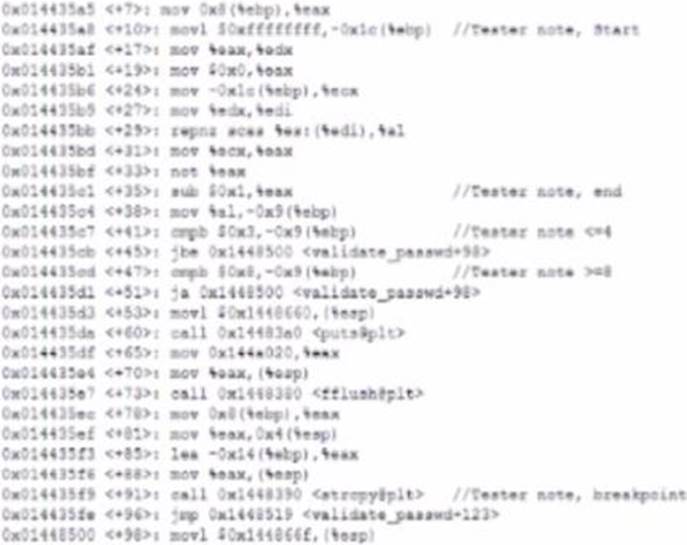
The penetration testers MOST likely took advantage of:
- A . A TOC/TOU vulnerability
B. A plain-text password disclosure
C. An integer overflow vulnerability
D. A buffer overflow vulnerability
Suggested Answer: A
Posted : 19/11/2022 4:52 pm
